Security vendors are everywhere, coming out of the woodwork. A fast growing segment of IT will yield significant investment from VCs looking to identify a rising star that has an angle on data protection that will be valuable to the market. The volume of products and services and the overlap can be overwhelming. The reality is many products and services can be valuable if implemented correctly, and many can fall short of expectations without the proper investment in people and process to run them. Enter PTP’s SOC Services powered by SOAR.
PTP has built a Security Orchestration Automation and Response (SOAR) platform compiled a set of tools for threat detection and response. Our SOAR platform yields immense value at a highly competitive cost which is critical to our customers who are growing and lack significant budgets for data security and security monitoring. Our recipe follows the NIST framework focusing and the segments of Identify, Protect, Detect, Respond and Recover. This discussion will focus on the platform used by PTP for “Detect” and how we gather data from our customers’ data protection tools and systems and analyze that data to make intelligent decisions on risks for breach.
Logs, Parsing, Rules, ML & Alerting
SIEMs (Security Information and Event Management) have been around for quite a while. Early versions of SIEMs were created in large part to address log management and storage requirements from the Payment Card Industry Data Security Standards (PCI DSS). These systems could parse logs from servers, firewalls and other devices and could provide retention of those logs, reporting of what was retained, and with some struggle, they could allow Security Operations Center (SOC) teams to search the logs. Newer versions, or Next Generation SIEMs, have improved the parsing of disparate logs, include faster databases for searching, archive older logs and have included rule sets and machine learning (ML) for the correlation of logs and the evaluation of indicators of compromise (IOCs). PTP leverages Fluency Security for our SIEM platform for a number of significant reasons that include: parsing ability, threat hunting, speed of searches, extensive rule set for ML, ability for API integration and working relationship with Fluency leadership. The image below outlines the workflow of Fluency from receipt of logs and data from datasources through it’s process of making decisions on events becoming security incidents.

Making the SIEM Part of a SOAR
PTP’s SOAR (Security Orchestration Automation and Response) implementation consists of a select group of tools and technologies. PTP leverages the platform along with our people and processes to assist in incident investigations, automate incident response and remediation, and provide our security analyst with a single point of visibility for events, threat intelligence and sharing.
The SOAR environment is utilized to reduce repetitive actions, automate analysis, and provide the correlation of observables across the PTP customer environments. It is a core platform that helps the SOC respond to incidents by providing standardization of data types, tagging of findings, and analysis of observations.
The environment consists of four highly integrated platforms depicted below.

The Hive
The Hive is a Security Incident Response Platform (SIRP). A system whose purpose is to assist incident responders with investigations and to make data readily available for analysis. The Hive is the integration point with PTP’s ISTM (ConnectWise) to communicate updates and status information between the SIRP and the ticketing system.
Cortex
Cortex is an analysis and active response engine. This process engine performs the heavy lifting when analysis of observables or handling of responders is required. Cortex comes with a base of over a hundred analyzers that can be applied to observable data covering a wide range of indicator types.
MISP
MISP is a Threat Intelligence Platform (TIP). This platform is used world-wide for sharing, storing, and correlating cyber security indicators across the security intelligence community. It is utilized to standardize the communication of these indicators and provide a key framework for communicating that information.
Shuffle
Shuffle is an automation and response platform. Shuffle bridges the gap between the components above and disparate systems, applications, and code. It provides an interface with APIs, a modular coding environment, and workflow for automation of actions, responses, and scheduling of repetitive tasks.
Process Integration
The main interface for the SOAR environment is through The Hive. User access requires a client VPN connection to the AWS VPC containing the SOAR components. The interface is browser-based and integrated with SSO for authorization and authentication.
When a Fluency alert is generated, the PeakPlus integration backend will create a ticket in ConnectWise and a corresponding case in The Hive that is prepopulated with data from the event. This helps accelerate the incident investigation and populates the case with standard types of data. SOC personnel are then free to begin running automations and data gathering tasks on the data, follow the deep link into Fluency to the triggering alert, and add other data or observations to the case as it progresses.
PTP SOAR In Action
Once an incident ticket is created, it is immediately apparent if any of the data correlates to other cases in the system and the status of those cases. See below.

Next, the list of related incidents can be expanded immediately to see exactly what observation details match with the current case to assist in handling of the ticket.

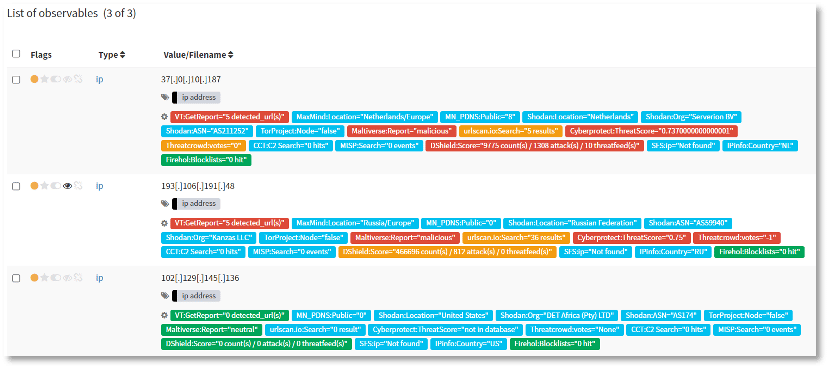
As seen in these images, tagging is heavily utilized to make sense of the data by pulling things together and increasing the visibility of important factors. The power of this feature combined with workflow automation is very apparent when dealing with lists of IP addresses from incident investigations. The data in the image below represents the results of triggering the automated tasks against a list of addresses. This workflow completed 24 searches against disparate sources for each IP address in the list within a couple of minutes and provides highly visible feedback to the analyst about them.
While the Hive is the main interface and most visible part of the environment, Cortex is tightly integrated with it to perform the heavy lifting. All the automation performed for the workflows is handed off to Cortex for processing and analysis. The results are then handed back to The Hive for collation, tagging, and tracking.
Both components communicate with MISP. MISP is used because “nobody knows everything, but everyone knows something”. MISP contains the current state of public knowledge about the world of security at large and is used to mine that data for IOCs. Our MISP is currently monitoring 47 data feeds covering 56 Galaxies (large data-object clusters) and 127 data taxonomies (namespaces). It encompasses data sets from such things as blocklists and Tor exit nodes, telemetry data on active APT groups, and malware indicators. These feeds are curated to reduce overlap and cast as wide a net as possible.
Summary
Security monitoring is about finding the needle in the haystack. Effective protection tools block the majority of activity, but it is the covert behavior that can cause the greatest harm, with malware sitting dormant in an environment until it is time for it to act. The combination of intelligent tools architected together in PTP’s SOAR environment allows the platform to sift through the massive volumes of event data and present to the security analyst those high risk items that require further investigation, and when doing so, determine if those activities are present in other monitored customer environment.
Want to take our services for a test drive? Click HERE for information on a FREE Proof of Concept!